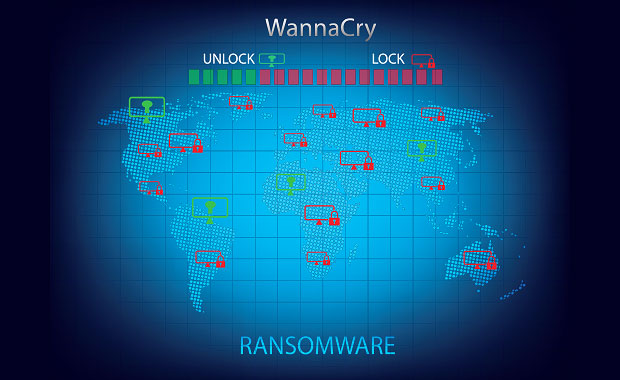
Government on Friday mentioned they have been investigating a large ransomware assault that reportedly hit greater than 45,000 computer systems in 74 international locations international, together with the United Kingdom’sNHS England nationwide well being provider, global supply provider FedEx, and Spanish telecom company Telefonica.
Safety mavens have connected the exploit to an previous leak by way of the Shadow Agents, who allegedly accessed a trove of hacking gear from the Nationwide Safety Company.
No Affected person Care Disaster
In accordance with early data, quite a few organizations reported that they have been suffering from a ransomware assault connected to the Wanna Decryptor, mentioned NHS Virtual spokesperson Tom Donnelly.
There used to be no instant proof that affected person information used to be breached, he mentioned, however the NHS used to be running with quite a lot of organizations to verify that.
The NHS used to be running with the Nationwide Cyber Safety Centre, the Division of Well being, and NHS England to give a boost to the affected organizations and counsel steps to mitigate the wear and tear, in line with Donnelly.
Sufferers who want emergency care will have to discuss with A&E or get admission to emergency services and products the similar approach they usually would, mentioned Anne Rainsberry, NHS incident director.
There are “attempted and examined” contingency plans to take care of this incident, she added.
The brunt of the assault used to be felt in Russia, and the Russian Inner Ministry posted a observation confirming that it had localized an assault on hundreds of private computer systems, Kaspersky Lab reported.
Spain’s Nationwide Cybersecurity Institute showed that quite a few corporations have been centered. Telefonica, the rustic’s biggest telephone corporate, showed that some computer systems on its inside company community have been hit, nevertheless it didn’t supply main points.
Microsoft Hyperlink
The ransomware assault is connected to the WannaCry ransomware circle of relatives, and it’s spreading aggressively world wide to different organizations, mentioned Adam Meyers, vice chairman of intelligence at CrowdStrike.
The assault so far reportedly has breached telecom techniques, hospitals, medical doctors’ surgical procedures, healthcare organizations, and fuel and electrical utilities in different Ecu and Asian international locations, starting from the United Kingdom to Russia, Pakistan, Spain and others, he famous.
“The crowd in the back of the assault does no longer seem to be choosy in regards to the country or sector it’s concentrated on,” Meyers advised the E-Trade Instances.
The assault vector has “all of the hallmarks of a standard pc malicious program,” he famous, including that prior to now CrowdStrike had no longer noticed a large-scale ransomware marketing campaign that used a self-propagating methodology at this scale, which makes this assault distinctive.
The sufferers most probably were centered in bulk thru huge phishing campaigns, turning in .zip archives with faux invoices, activity gives, safety warnings and undelivered mail, Meyers mentioned.
Wana encrypts information the use of the AES-128 cipher and calls for a bitcoin ransom that will increase as time passes on, in line with Meyers. The information are appended with a .wncry record extension. Calls for from this assault come with requests for US$300 or $600 in bitcoin for a decryption key.
Corporations will have to set up ransomware prevention and gadget finding out gear, Pattern Micro advisable. The company additionally steered set up of MS17-010, a important safety patch Microsoft issued in March.
Probably the most serious of the vulnerabilities may permit far off code execution, in line with the Microsoft bulletin, if an attacker will have to ship specifically crafted messages to a Microsoft server message block 1.0 (SMBv1) server.
Place of origin Protected
“We’re acutely aware of studies of ransomware affecting a couple of entities in Europe and Asia and are coordinating with our global cyber companions,” DHS spokesperson Scott McConnell advised the E-Trade Instances in a observation.
The DHS “stands in a position to give a boost to any global or home spouse’s request for help,” he added, noting that the company automatically supplies cybersecurity help upon request, together with “technical research and give a boost to.” Data shared with DHS as a part of those efforts is confidential.
Supply Via https://www.technewsworld.com/tale/british-hospitals-fedex-among-thousands-hit-by-ransomware-84529.html